DeepSeek’s privacy practices have come under scrutiny as its popularity surges, prompting users to wonder how DeepSeek’s privacy protocols stack up against other AI applications. At COMPARE.EDU.VN, we provide a detailed analysis to help you understand the data handling of different AI apps. This comprehensive comparison will look beyond surface-level privacy policies and investigate the real-world data practices, offering insights into user data protection, data security measures, and potential privacy concerns.
1. Introduction: DeepSeek’s Rise and Privacy Concerns
DeepSeek, launched on January 10, 2025, by a Chinese developer, rapidly ascended to become a leading AI application, surpassing even ChatGPT in popularity on both the Google Play Store and Apple’s App Store. However, this meteoric rise has been accompanied by significant concerns from privacy experts. These experts are particularly focused on the extent of data collection by DeepSeek and the possibility of this data being shared with servers located in China. The issues extend beyond mere data handling to encompass aspects of alignment and censorship, making a thorough evaluation of its privacy policy essential.
2. The Need for a Comparative Analysis
The digital landscape is increasingly populated with AI-driven applications, each promising innovative solutions and enhanced user experiences. However, the underlying data practices of these applications often remain opaque, leaving users vulnerable to potential privacy breaches. Understanding how different AI apps handle user data is crucial for making informed decisions about which apps to trust and use.
3. Focus on DeepSeek: A Closer Look
DeepSeek’s rapid ascent in the AI app market has brought its privacy practices under intense scrutiny. The core issues revolve around the type and volume of user data collected and the potential for this data to be transmitted to servers in China. Concerns about alignment, which refers to ensuring that AI behavior is consistent with human values and intentions, and censorship, which raises questions about the app’s content filtering policies, add further complexity to the evaluation of DeepSeek’s privacy posture.
4. Objective: Beyond the Privacy Policy
While privacy policies offer a glimpse into an application’s data handling practices, they often present an incomplete or idealized picture. Privacy policies may be overly broad, encompassing potential future data collection activities, or too narrow, omitting details about actual data sharing practices. This necessitates a deeper dive into the application’s operations to uncover the reality of its data handling. COMPARE.EDU.VN goes beyond mere policy statements, focusing on real-world evidence to assess the true privacy implications of using DeepSeek.
5. Methodology: Evaluating Mobile App Privacy
COMPARE.EDU.VN employs a rigorous methodology to evaluate the privacy posture of mobile applications. This approach focuses on several critical criteria, providing a comprehensive assessment of data handling practices.
5.1. Permissions Requested
The first aspect of evaluation involves scrutinizing the permissions an application requests from users. Permissions such as access to location, microphone, and camera provide insight into the app’s capabilities and potential data collection activities. The evaluation considers the purpose and implications of each permission, assessing whether the app’s functionality justifies the level of access requested.
5.2. Third-Party SDKs Integrated
The presence of third-party Software Development Kits (SDKs) within an application can significantly impact its privacy posture. These SDKs, often used for analytics or advertising purposes, may collect user data independently of the main application. The evaluation identifies the SDKs included in the app and assesses the types of data they typically collect.
5.3. Data Collection Practices
Identifying the specific user and device data that an application collects is essential for understanding its privacy implications. This includes personal information, usage patterns, and location data. The evaluation focuses on determining what data is collected, how it is collected, and the purposes for which it is used.
5.4. Data Sharing with Third Parties
The entities with whom an application shares user data can significantly impact its privacy posture. This includes ad networks and analytics providers. The evaluation identifies the third parties receiving user data and assesses their privacy policies and data handling practices.
5.5. Cross-Border Data Transfers
The transfer of user data to countries outside the user’s home region raises compliance and regulatory concerns. Different countries have varying data protection laws, and transferring data to jurisdictions with weaker protections can increase privacy risks. The evaluation determines whether the application sends data to countries outside the user’s home region and assesses the potential implications.
5.6. Consistency Between Policy and Practice
The final aspect of the evaluation involves comparing the application’s privacy policy with its actual data handling practices. Any discrepancies or gaps between the policy and the observed practices raise concerns about transparency and trustworthiness. The evaluation identifies any mismatches and assesses their significance.
6. DeepSeek App: An In-Depth Analysis
According to the research, DeepSeek’s privacy policy is broadly defined, covering all potential data collection scenarios, including sensitive data like keystrokes. However, the study found that DeepSeek collects less data than what it states in its privacy policy, although it does send data to China. The app asks for eight permissions, one of which is the sensitive Camera permission. It gathers data such as unique IDs, device information, location (time zone), language, and user inputs, like prompts or chat history. This data is shared with major companies like Google (US) and ByteDance (China). Additionally, the app uses SDKs from Google, Tencent, and ByteDance for authentication, analytics, and marketing.
7. Permissions DeepSeek Requires
DeepSeek requests a total of eight permissions, including one sensitive permission.
| Data Types | Permissions | Sensitive Permissions | Description |
|---|---|---|---|
| Photos and Videos | android.permission.CAMERA | android.permission.CAMERA | Allows the app to capture photos or videos using the device’s camera. |
| Device or Other IDs | com.asus.msa.SupplementaryDID.ACCESS | (None) | Potentially grants access to unique device identifiers on certain ASUS devices. |
| App Info & Performance | android.permission.FOREGROUND_SERVICE, android.permission.ACCESS_NETWORK_STATE, android.permission.ACCESS_WIFI_STATE, android.permission.INTERNET, com.android.vending.CHECK_LICENSE, com.deepseek.chat.DYNAMIC_RECEIVER_NOT_EXPORTED_PERMISSION | (None) | These permissions allow the app to run tasks in the foreground, check or use network connections, and verify licenses. While they do not directly collect personal data, they can facilitate background processes and data transfers. |
8. SDKs Embedded in DeepSeek
DeepSeek app embeds SDKs from Google, Tencent, Bytedance and transfers data to third parties based out of China.
| SDK | Third Party | Location | Purpose | Description (Lawyer-Friendly) |
|---|---|---|---|---|
| com.deepseek.chat.wxapi.WXEntryActivity | WeChat (Tencent) | China | Authentication | Integrates WeChat social login. Not available while testing from the USA. |
| com.google.android.gms.common.api.GoogleApiActivity | United States | Developer/Framework | Part of Google Play Services. Supports various Google APIs for app functionality and updates. | |
| com.google.android.gms.auth.api.signin.internal.SignInHubActivity | United States | Authentication | Google Play Services SDK for user sign-in. | |
| com.google.android.gms.auth.api.signin.RevocationBoundService | United States | Authentication | Manages revocation of user sign-in tokens. Involves account data processed through Google servers. | |
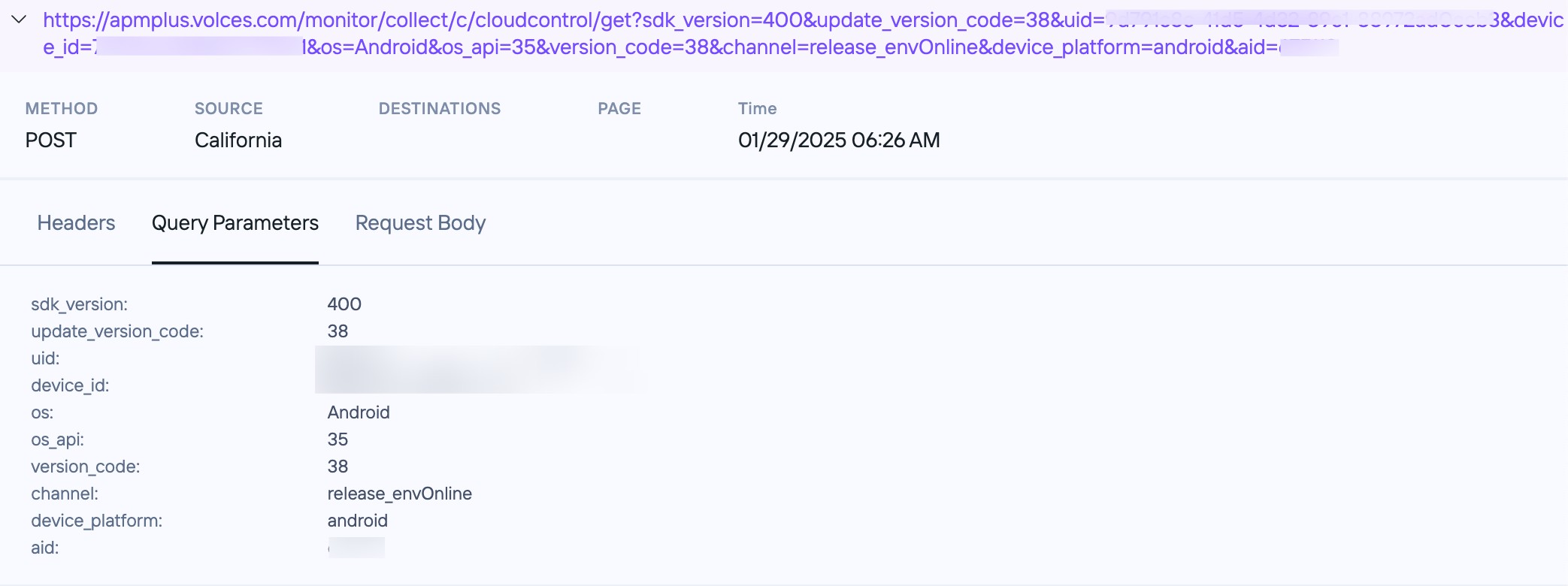
| com.bytedance.applog.migrate.MigrateDetectorActivity | Volcengine (ByteDance) | China | Marketing / Growth / Analytics | Bytedance AppLog SDK, which can collect user engagement or behavioral data. |
| com.bytedance.apm6.traffic.TrafficTransportService | Volcengine (ByteDance) | China | Unknown / Possibly Analytics | Unknown |
| com.bytedance.applog.collector.Collector | Volcengine (ByteDance) | China | Marketing / Growth / Analytics | Collects usage and performance data. May be used for user segmentation, marketing optimization, or analytics. |
| com.bytedance.frameworks.core.apm.contentprovider.MonitorContentProvider | Volcengine (ByteDance) | China | Unknown / Possibly Monitoring | Unknown |
| com.google.android.play.core.common.PlayCoreDialogWrapperActivity | United States | Developer/Framework | Google Play Core Library. Typically handles in-app updates and user prompts. Minimal direct user data collection. |
9. Types of Data Collected by DeepSeek
Deep Seek collects unique identifiers, device identifiers, device details(model name, OS), user input – prompts, text, audio, image data which is transferred to China both internally and to third parties.
| Data Type | Variables/Values | Shared with |
|---|---|---|
| Unique Identifiers | Iid, aid, x-rangers-id, chat_session_id | volces.com (China, Bytedance), deepseek.com (China), googleapis.com (US), fengkongcloud.com (China) |
| Device Information | User-Agent, Device Model, OS, Android Version | volces.com (China, Bytedance), deepseek.com (China), googleapis.com (US), fengkongcloud.com (China), gvt2.com (US) |
| Location – State | America/Los_Angeles | googleapis.com (US) |
| Language | en-us | deepseek.com (China), googleapis.com (US) |
| User Input | prompt, file-id, chat-session-id | deepseek.com (China) |
10. Third Parties Involved with DeepSeek
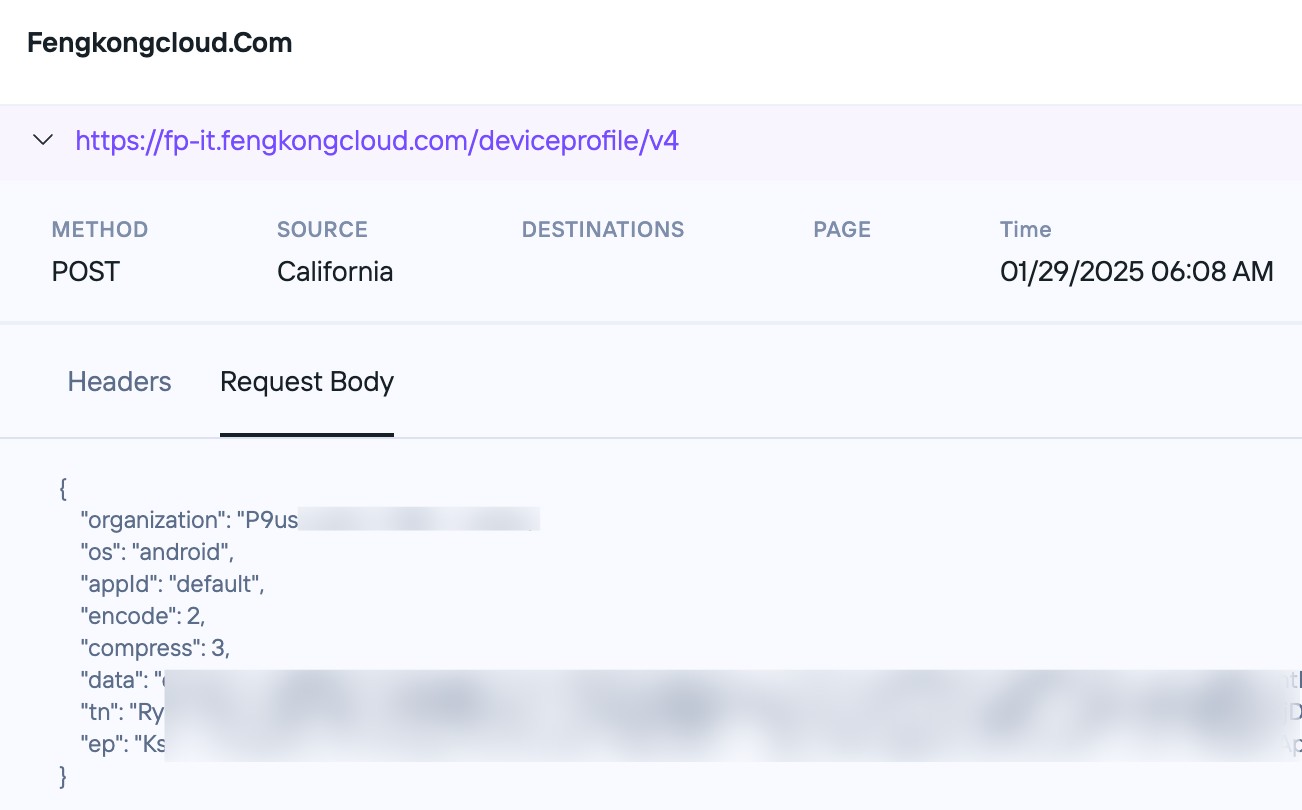
DeepSeek integrates with 4 third parties including volces.com(Volcengine by Bytedance) and fengkongcloud.com(by ishumei.com) where data is shared to China.
| Third Party | Location | Data Type Shared |
|---|---|---|
| volces.com – Volcengine by Bytedance | China | Unique Identifiers (Device ID), Device Information |
| gvt2.com | US | Device Information |
| googleapis.com | US | Unique Identifiers, Device Information, Language, Location – State |
| fengkongcloud.com | China | Unique Identifiers, Device Information |
11. Discrepancies in DeepSeek’s Privacy Policy
| Category | Evidence Found | Privacy Policy Disclosure | Observation |
|---|---|---|---|
| Unique Identifiers | unique_identifier, aid, device_id, chat_session_id | Disclosed broadly under “Automatically Collected Information” as unique device identifiers, user IDs, and related data. | Aligned: The policy broadly covers unique identifiers. |
| Device Information | device_info (e.g., model, OS version) | Disclosed broadly under “Technical Information” as device model, operating system, and related technical details. | Aligned: Policy covers device information comprehensively, matching our tests. |
| Network Data | IP address, request headers (e.g., Content-Type, Authorization, User-Agent), and API calls. | Disclosed broadly under “Technical Information”. | Aligned. |
| Keystroke Data | Not Found in Evidence | Disclosed under “Technical Information” as keystroke patterns or rhythms. | Overdisclosed: Keystroke data was not observed in our tests but is included in the privacy policy, making it broader than the actual data collected. |
| Location Data | Approximate location (e.g., America/Los_Angeles) | Disclosed broadly under “Technical Information” and “Permissions” as general location and system language. | Aligned: General location data is covered, but the policy is broader, suggesting more granular location data could be collected (e.g., GPS or geolocation). |
| User Input | Chat prompts, uploaded files, chat history | Disclosed under “User Input” as content provided by users, including text, files, and history. | Aligned: Policy matches evidence provided. |
| Error and Debug Data | Debugging details such as status_code (429) and server_ip (192.178.130.102). | Disclosed broadly under “Service-Related Data” as diagnostic and performance information, including crash reports. | Partially Aligned: Policy broadly covers debugging information, but specific data like status_code and server_ip are not explicitly mentioned. |
| Application Metadata | sdk_version, os_api, channel, version_code | Disclosed under “Technical Information” as app and device metadata. | Aligned: Policy matches evidence provided. |
| Payment Data | Not Found in Evidence | Disclosed under “Payment Information” as order and transaction history for paid services. | Not tested. |
| Advertising Data | Not Found in Evidence | Disclosed under “Advertising and Analytics Partners” as advertising identifiers, hashed email addresses, and cookies. | Overdisclosed: Advertising data is disclosed but not present in our tests. |
12. Privacy Concerns Summary for DeepSeek
The primary privacy concerns regarding DeepSeek involve data transfers to China, both to its servers and third-party SDKs integrated into the app. While the privacy policy is broadly written and keystroke tracking was not observed during testing, there remains a potential for excessive data collection as the app evolves.
13. DeepSeek Testing Methodology
Privado’s Mobile App Scanning product simulates user interactions with the app from various locations. The tests on DeepSeek were conducted from California, using the latest version of the app on the Play Store as of January 27, 2025. The analysis was done purely for research purposes to uncover privacy practices of DeepSeek app.
14. How DeepSeek Compares to Other AI Apps: ChatGPT, Claude, and Perplexity
To provide a broader context for understanding DeepSeek’s privacy practices, it is essential to compare it with other prominent AI applications such as ChatGPT, Claude, and Perplexity. Each of these applications has its unique approach to data handling, and a comparative analysis can reveal important distinctions and commonalities.
14.1. ChatGPT: Privacy Practices
ChatGPT, developed by OpenAI, has gained widespread popularity for its ability to generate human-like text and engage in conversations. However, its privacy practices have also been subject to scrutiny. Key aspects of ChatGPT’s privacy approach include:
- Data Collection: ChatGPT collects user input, including prompts and generated text, which is used to train and improve its models. It also collects device information, such as IP addresses and browser types.
- Data Usage: The collected data is primarily used for model training, research, and development purposes. OpenAI states that it takes measures to anonymize and aggregate data to protect user privacy.
- Data Sharing: OpenAI may share data with third-party service providers who assist in providing and maintaining the ChatGPT service.
- Privacy Policy: OpenAI’s privacy policy outlines its data handling practices and provides users with choices regarding their data, such as the ability to opt out of data collection for model training.
14.2. Claude: Privacy Practices
Claude, developed by Anthropic, is another AI assistant designed to engage in conversations and perform various tasks. Its privacy practices include:
- Data Collection: Claude collects user input, device information, and usage data. The data collected is used to improve the model and provide personalized experiences.
- Data Usage: Anthropic uses collected data for model training, research, and development purposes. It also employs data anonymization and aggregation techniques to protect user privacy.
- Data Sharing: Anthropic may share data with third-party service providers who assist in delivering and improving the Claude service.
- Privacy Policy: Anthropic’s privacy policy details its data handling practices and provides users with options to manage their data.
14.3. Perplexity: Privacy Practices
Perplexity AI is an AI-powered search engine that provides users with concise and accurate answers to their queries. Its privacy practices include:
- Data Collection: Perplexity collects user queries, device information, and location data. The data collected is used to improve search results and provide personalized recommendations.
- Data Usage: Perplexity uses collected data for search result optimization, research, and development purposes. It also employs data anonymization and aggregation techniques.
- Data Sharing: Perplexity may share data with third-party service providers who assist in delivering and improving the search engine service.
- Privacy Policy: Perplexity’s privacy policy outlines its data handling practices and provides users with choices regarding their data.
15. Comparative Analysis Table
To facilitate a clear comparison of the privacy practices of DeepSeek, ChatGPT, Claude, and Perplexity, the following table summarizes the key aspects of each application’s data handling.
| Feature | DeepSeek | ChatGPT | Claude | Perplexity |
|---|---|---|---|---|
| Data Collection | User input, device info, unique IDs, location | User input, device info | User input, device info, usage data | User queries, device info, location data |
| Data Usage | Model training, analytics | Model training, research | Model training, research | Search optimization, research |
| Data Sharing | Third-party SDKs, ByteDance, Google | Third-party service providers | Third-party service providers | Third-party service providers |
| Cross-Border Data Transfer | China, US | Varies | Varies | Varies |
| Privacy Policy | Broad, covers various data types | Outlines data handling practices | Details data handling practices | Outlines data handling practices |
| Key Concerns | Data transfer to China | Model training data usage | Model training data usage | Search query privacy |
16. Key Differences and Similarities
The comparative analysis reveals several key differences and similarities among the privacy practices of these AI applications.
16.1. Data Collection Scope
DeepSeek collects a broader range of data, including unique identifiers and precise location data, compared to the other applications. ChatGPT, Claude, and Perplexity primarily focus on collecting user input and device information.
16.2. Data Usage Transparency
ChatGPT, Claude, and Perplexity provide more transparency regarding their data usage practices, particularly in relation to model training and research. DeepSeek’s data usage practices are less clearly defined.
16.3. Data Sharing Practices
DeepSeek shares data with a wider range of third parties, including ByteDance and Google, compared to the other applications, which primarily share data with service providers.
16.4. Cross-Border Data Transfers
DeepSeek’s data transfer to China raises unique privacy concerns due to China’s data protection laws. The other applications’ data transfer practices vary depending on the location of their users and service providers.
16.5. Privacy Policy Specificity
DeepSeek’s privacy policy is broader and covers a wider range of data types, while the other applications have more specific policies outlining their data handling practices.
17. Implications for Users
The differences in privacy practices among these AI applications have significant implications for users. Users who prioritize data privacy may prefer applications with more transparent data usage practices and limited data sharing. The risk of cross-border data transfers, especially to jurisdictions with weaker data protection laws, may also be a factor in users’ choices.
18. Recommendations for Choosing an AI App
When choosing an AI app, users should carefully consider their privacy preferences and the data handling practices of the applications they are considering. Key recommendations include:
- Review the privacy policies: Carefully read and understand the privacy policies of each application to understand their data collection, usage, and sharing practices.
- Consider data sensitivity: Evaluate the types of data the application collects and whether the collection is necessary for the app’s functionality.
- Assess data sharing practices: Determine with whom the application shares data and whether the third parties have adequate data protection measures in place.
- Evaluate cross-border data transfers: Consider the implications of data transfers to countries with different data protection laws.
- Look for transparency: Choose applications that provide clear and transparent explanations of their data handling practices.
- Use privacy-enhancing tools: Utilize privacy-enhancing tools, such as VPNs, to protect your data when using AI applications.
19. The Role of COMPARE.EDU.VN
COMPARE.EDU.VN is committed to providing users with the information they need to make informed decisions about their privacy. Our detailed comparative analyses of AI applications empower users to choose apps that align with their privacy preferences and provide a safe and secure user experience.
20. Staying Informed
The digital landscape is constantly evolving, and AI applications are continuously updating their data practices. It is essential to stay informed about the latest privacy developments and regularly review the privacy policies of the applications you use.
21. Conclusion: Making Informed Choices
Choosing an AI application involves carefully considering its privacy practices. By understanding the data handling of different apps and prioritizing your privacy preferences, you can make informed choices that protect your data and enhance your user experience. COMPARE.EDU.VN is here to guide you through this process, providing you with the insights you need to navigate the complex world of AI privacy.
Prioritize your privacy by making informed decisions based on detailed comparisons at COMPARE.EDU.VN. Don’t navigate the complex world of AI privacy alone; visit COMPARE.EDU.VN today to explore comprehensive comparisons and make choices that align with your values. Discover objective analyses, detailed feature comparisons, and user reviews—all in one place. Make your decision easier and more informed with COMPARE.EDU.VN, located at 333 Comparison Plaza, Choice City, CA 90210, United States. Contact us via Whatsapp at +1 (626) 555-9090 or visit our website COMPARE.EDU.VN for more information.
22. FAQs About AI App Privacy
22.1. What is an AI app privacy policy?
An AI app privacy policy is a legal document that outlines how an AI application collects, uses, and shares user data. It provides users with information about their rights and choices regarding their data.
22.2. Why is it important to read an AI app privacy policy?
Reading an AI app privacy policy is important because it helps you understand how your data is being handled and allows you to make informed decisions about whether to use the app.
22.3. What are the key elements of an AI app privacy policy?
Key elements of an AI app privacy policy include: the types of data collected, how the data is used, with whom the data is shared, cross-border data transfers, and user rights and choices.
22.4. How can I compare the privacy policies of different AI apps?
You can compare the privacy policies of different AI apps by reviewing their data collection, usage, and sharing practices. Look for applications with transparent policies and limited data sharing.
22.5. What are the risks of using an AI app with a poor privacy policy?
Risks of using an AI app with a poor privacy policy include: data breaches, unauthorized data sharing, and loss of control over your personal information.
22.6. How can I protect my privacy when using AI apps?
You can protect your privacy when using AI apps by reviewing privacy policies, limiting data sharing, using privacy-enhancing tools, and staying informed about privacy developments.
22.7. What are some common data collection practices of AI apps?
Common data collection practices of AI apps include: collecting user input, device information, location data, and usage data.
22.8. How do AI apps use my data?
AI apps use your data for purposes such as: model training, research, development, search optimization, and personalization.
22.9. What are my rights regarding my data under AI app privacy policies?
Your rights regarding your data under AI app privacy policies may include: the right to access your data, the right to correct inaccuracies, the right to delete your data, and the right to opt out of data collection.
22.10. Where can I find reliable information about AI app privacy?
You can find reliable information about AI app privacy at compare.edu.vn, which provides detailed comparative analyses of AI applications.
